Moyra Schauffler
During the years prior to American entry into World War II (WWII), president Franklin Delano Roosevelt’s (FDR) actions show his instinct of eventual American participation in the war combined with his practical resolve to keep the country neutral until both Congress and the public would be supportive of involvement. Beginning with the Munich Conference and the subsequent crisis of German appeasement, the president showcased his apprehensions of Adolf Hitler’s Germany while still trying to maneuver his country through an economic crisis and the isolationist tendencies that defined this moment in American history. As the war began with Hitler’s disregard for the agreements established in Munich and the Nazi invasion of Poland in September 1939, FDR reacted by showing his willingness to take steps to protect the Western Hemisphere, but continued to insist on American neutrality. When Hitler initiated the blitzkrieg, or “lightning war” on Western Europe in the spring of 1940, FDR immediately reacted by attempting to mobilize American popular opinion in the direction of support for the Allied Powers consisting of Great Britain, France, and the Soviet Union, among other smaller countries.
The American president’s consistent efforts to assist the Allies but remain out of the war resulted in the congressionally approved lend-lease bill in March 1941. The implementation of lend-lease increased American presence in the North Atlantic Ocean. The regular presence of United States (US) vessels unnerved German naval forces in the area, eventually leading to the USS Greer incident and the beginning of an undeclared naval war between the US and Germany. Finally, the entire progression of US preparation for entrance into WWII culminated with the Japanese attack on Pearl Harbor on December 7, 1941. The surprise attack on US soil pushed president Roosevelt to urge Congress to declare war on Japan and initiate a new era of American involvement in global affairs.
In order to demonstrate America’s complicated path to WWII, a map is helpful because it can clearly illustrate how global catastrophes lead to clear US reactions directly involving American diplomats and politicians. Overall, the map displays how FDR and the United States reacted in increasingly aggressive ways that eventually led to complete support and allegiance with the Allies. Each point on this interactive Google map represents an event or significant change in American foreign policy that led to entry into WWII. As is evident on the map, the most significant events occurred on either side of the Atlantic Ocean, with the exception of the attack on Pearl Harbor. That being said, other events occurred, which signaled another war on the horizon and accelerated US involvement, that are not displayed on the map. For example, Hitler’s 1935 announcement of rearmament in violation of the Treaty of Versailles, and FDR’s invocation of the Neutrality Acts in September 1939 in response to the start of WWII do not appear, but are still important to understanding the motivations and process the United States went through to prepare for war.
The first point on the map represents the Munich Conference on September 28, 1938 in Munich Germany. In his book entitled From Colony to Superpower, George Herring cites this conference and what later became known has the Munich Crisis, as a major turning point in FDR’s view and opinion on Hitler’s Germany. Herring says that, “Munich…convinced FDR that Hitler was responsible for Europe’s drift toward war and might be bent on world domination. The president was no longer casually confident of a British and French victory in the event of war”(Herring, 515). As this quote illustrates, the idea of German appeasement in Munich and Hitler’s apparent intentions of bringing the European continent to war concerned president Roosevelt. Herring goes on to explain how Munich forced the president to realize his country was no longer secured by its two-ocean buffer in the event Hitler chose to use military strength to harm the United States (Herring, 515). Hitler’s invasion of Poland in 1939 only reinforced FDR’s growing apprehensions.
On September 1, 1939, Hitler invaded Poland thereby beginning the second great European war. The place mark on the map sits on Wielun, Poland because the town was the first to encounter Nazi bombings. According to The Atlantic, Poland officially surrendered to the Germans in October 1939 after losing over 60,000 troops and thousands of civilians (Alan Taylor). Immediately following the invasion, on September 3rd, FDR gave a fireside chat entitled, “On the European War”. In this radio broadcast, the president encouraged his listeners to remember, “You must master at the outset a simple but unalterable fact in modern foreign relations between nations. When peace has been broken anywhere, the peace of all countries everywhere is in danger.” In this instance, the president recognized US abstinence from involvement in the European war, but he emphasized how interconnected the world was in the new era, and that the country could no longer remain unaffected by the conflict.
The next significant transition in this saga occurred in late September 1939 when the US attended a conference in Panama City with other Latin American countries, where they discussed neutrality, hemispheric security, and economic cooperation in connection to the war (Sanders, 232). The most significant agreement created at the conference, was the “Declaration of Panama”, in which the countries in attendance established a “neutrality zone” extending an average of three hundred miles around the hemisphere and thereby outlawing belligerent ships from committing hostile acts within the area (Herring, 528). This declaration is significant because it highlights a clear step towards American engagement in the European war by enforcing its neutrality through the zone encircling the Western Hemisphere.
In April 1940, with the initiation of the blitzkrieg in Europe, the bloodiest phase of the war began. As Hitler’s attacks shocked the world, FDR attempted to tip the balance of neutrality in favor of the Allies. The most significant of these attempts involved the president endorsing the creation of the Committee to Defend America by Aiding the Allies (CDA). As a way to mobilize public opinion in favor of the Allies, the CDA worked to “educate the nation about the fascist threat and mobilize backing for aid to Britain”(Herring, 521). Herring goes on to emphasize how the FDR administration, “furnished inside information, making it appear that the government was responding to popular demand…”(Herring, 521). The CDA provides a clear example of FDR maneuvering his country into supporting the Allies and thereby moving closer to war.
The critical turning point in American policy towards WWII occurred in March 1941, when Congress passed the Bill to Promote the Defense of the United States, better known as the Lend-Lease bill or HR-1776 (Herring, 525). Herring describes lend-lease as the opening of, “the nation’s warehouses to what was now a de facto ally and providing a mechanism for the first U.S. foreign aid program”(Herring, 525). With the implementation of lend-lease came increased US shipping in the North Atlantic Ocean. FDR mobilized the Atlantic Fleet on March 15, 1941 and made clear US intentions to protect lend-lease supplies going to Britain (Schuessler, 156). As lend-lease transports continued throughout the summer of 1941, tensions rose between the American and German vessels in the North Atlantic resulting in the USS Greer incident on September 4, 1941.
The undeclared naval war between the American and German naval forces in the North Atlantic began when a German U-boat launched a torpedo attack on the USS Greer. The torpedoes missed the American vessel, but after that incident several US ships, such as the Kearney and the Reuben James, sank from German torpedo hits (Freeland, 27 & 50). These attacks comprised the last phase of US “neutrality” in the war because three months after the first attack on the Greer, the Japanese executed their surprise attack on Pearl Harbor.

Image of FDR signing the declaration of war courtesy of Wikipedia
December 7, 1941 marked the day when the United States could no longer avoid becoming directly intertwined in the ongoing war in Europe and the Pacific. Herring describes Japan’s attack as, “…a desperate effort to solve their problems and, they hoped, intimidate the United States into acquiescing to their East Asian design, the Japanese mounted a bold attack by carrier aircraft against the U.S. naval and military bases at Pearl Harbor. They achieved complete surprise…with devastating results, killing 2,500 soldiers…” (Herring, 535). The attack prompted FDR to submit an immediate request for a congressional declaration of war and a radio address to assure the American people that justice would be served against the Japanese.
In total, the long process towards US involvement in WWII tells the story of how an isolationist nation transitioned to a role of global leadership thanks to the aggressive policies and rhetoric of its president, Franklin Delano Roosevelt. As FDR became aware of Hitler’s tyrannical actions, he stepped in, to at first defend the Western Hemisphere from harm and later to assist Great Britain and the Allies. Following the end of WWII, the nation would never return to the isolationist tendencies of the 1930s, and instead would become one of the most powerful countries in the world.
Works Cited
Herring, George C. From Colony to Superpower. New York: Oxford University Press, 2008.
Taylor, Alan. “World War II: The Invasion of Poland and the Winter War.” The Atlantic. June 26, 2011. http://www.theatlantic.com/infocus/2011/06/world-war-ii-the-invasion-of-poland-and-the-winter-war/100094/.
Sanders, William. “Consultation Among The American Republics.” World Affairs 102, no. 4 (December 1939): http://www.jstor.org/stable/20663342.
Schuessler, John M. “The Deception Dividend: FDR’s Undeclared War.” International Security 34, no. 4 (Spring 2010). Project Muse.
Freeland, Stephen. “‘Shoot on Sight!’: FDR and the Greer Incident.” Sea Classics 34, no. 9 (September 2001). Proquest Research Library.



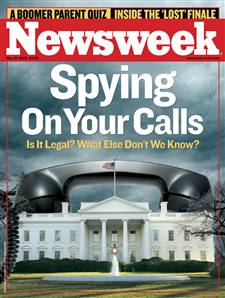
 The story of the Julius and Ethel Rosenberg might well be the most dramatic in the history of US national security. It involves so much –atomic weapons, espionage, treason, blackmail, high stakes legal drama, ethnic loyalties, political beliefs, family betrayal, marriage, friendship, and ultimately, death. Students in History 282 will be viewing a gripping documentary about the case by the Rosenberg’s granddaughter, Ivy Meer0pol. “Heir to an Execution” (2004) provides a unique insider’s view of the story, showing the filmmaker as she tries to come to terms with the legacy of the case for her own, broken family. They will then use the film to inspire their own reflections on the challenges of balancing liberty with security in age of almost perpetual war.
The story of the Julius and Ethel Rosenberg might well be the most dramatic in the history of US national security. It involves so much –atomic weapons, espionage, treason, blackmail, high stakes legal drama, ethnic loyalties, political beliefs, family betrayal, marriage, friendship, and ultimately, death. Students in History 282 will be viewing a gripping documentary about the case by the Rosenberg’s granddaughter, Ivy Meer0pol. “Heir to an Execution” (2004) provides a unique insider’s view of the story, showing the filmmaker as she tries to come to terms with the legacy of the case for her own, broken family. They will then use the film to inspire their own reflections on the challenges of balancing liberty with security in age of almost perpetual war.